The Zero-Day Singularity
How 2026’s Vulnerability Heatmap Proves Human-Speed Defense is Mathematically Obsolete
As we digest the Q1 2026 telemetry across the global threat landscape, one uncomfortable truth becomes impossible to ignore: the corporate digital perimeter is a psychological crutch, not a physical reality. Boardrooms across the Fortune 500 have spent the last decade trapped in an escalating arms race, assuming that a larger cybersecurity budget linearly translates to a reduced risk of a breach. But the heatmap of current vulnerabilities reveals a fundamentally different mathematical reality. We are no longer dealing with a defense-in-depth scenario; we are operating within an asymmetric game of exponential exposure.
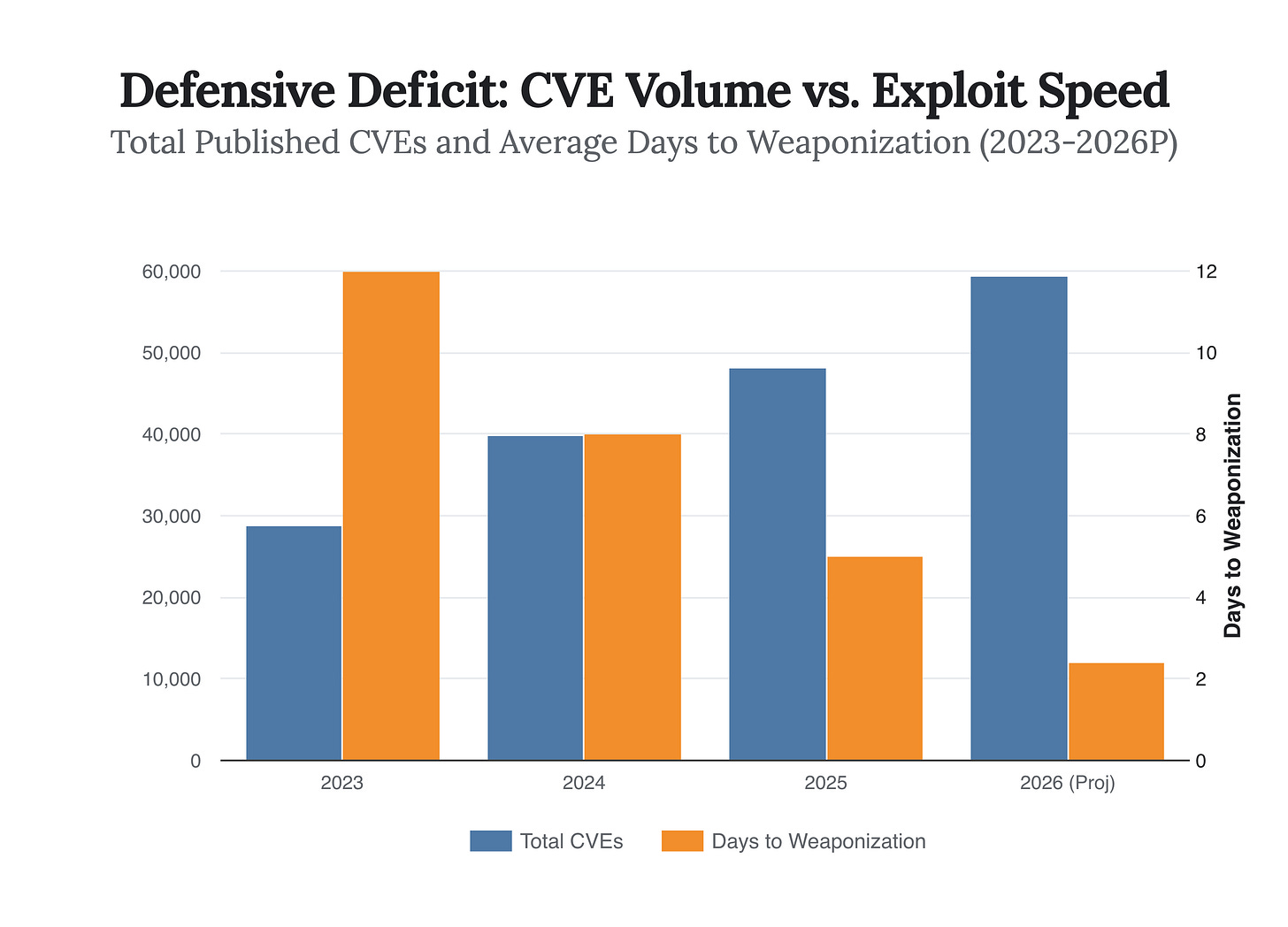
In 2025, the global cybersecurity apparatus recorded an unprecedented 48,185 Common Vulnerabilities and Exposures (CVEs). That represents a staggering 20.6% year-over-year surge, equating to exactly 133 new foundational flaws entering the wild every single day. As of April 2026, predictive models from FIRST indicate this trajectory is accelerating, projecting a median of 59,427 new CVEs by year’s end.
If security teams are forced to play “whack-a-mole” with 133 new vulnerabilities a day, the strategy of patching everything systematically collapses under its own weight. But raw volume is merely a vanity metric for the uninitiated; the true strategic peril lies in the velocity of weaponization.
The Arithmetic of Weaponization and The Death of Time
The strategic leverage in cybersecurity has historically been defined by time—specifically, the window between a vulnerability’s disclosure and its active exploitation in the wild. For years, organizations could rely on a comfortable buffer to test patches without breaking production environments. That buffer has now evaporated. According to the latest 2026 vulnerability analytics, the average time from a vulnerability’s discovery to a public exploit has plummeted to a mere 2.4 days.
Yet, the speed of exploitation is only half the equation. The arrival of deeply integrated, offensive AI has fundamentally altered the threat actor’s operational tempo. AI-enabled adversaries have increased their attack volume by 89% year-over-year, automating the tedious reconnaissance phases that used to stall human hackers. The result is a total collapse of the “breakout time”—the crucial window between an attacker gaining initial access and moving laterally across a network to lock down critical infrastructure.
According to 2025 telemetry, the average eCrime breakout time fell to just 29 minutes, with the fastest recorded instance clocking in at an apocalyptic 27 seconds.
In an era where the average eCrime breakout time has plummeted to just 29 minutes, traditional human-speed incident response is mathematically obsolete.
If your defensive posture relies on a human analyst receiving a SIEM alert, digesting the log data, and manually isolating a compromised endpoint, the game is already lost. By the time the analyst finishes their coffee, the adversary has already extracted your proprietary data and encrypted the central backups. The strategic equilibrium has shifted entirely. The attacker’s marginal cost of executing an attack is approaching zero, while the defender’s cost of preventing every single one is approaching infinity.
Unlock deeper strategic alpha with a 10% discount on the annual plan.
Support the data-driven foresight required to navigate an era of radical uncertainty and join a community of institutional-grade analysts committed to the truth.
The Privatization of Elite Cyber Weapons
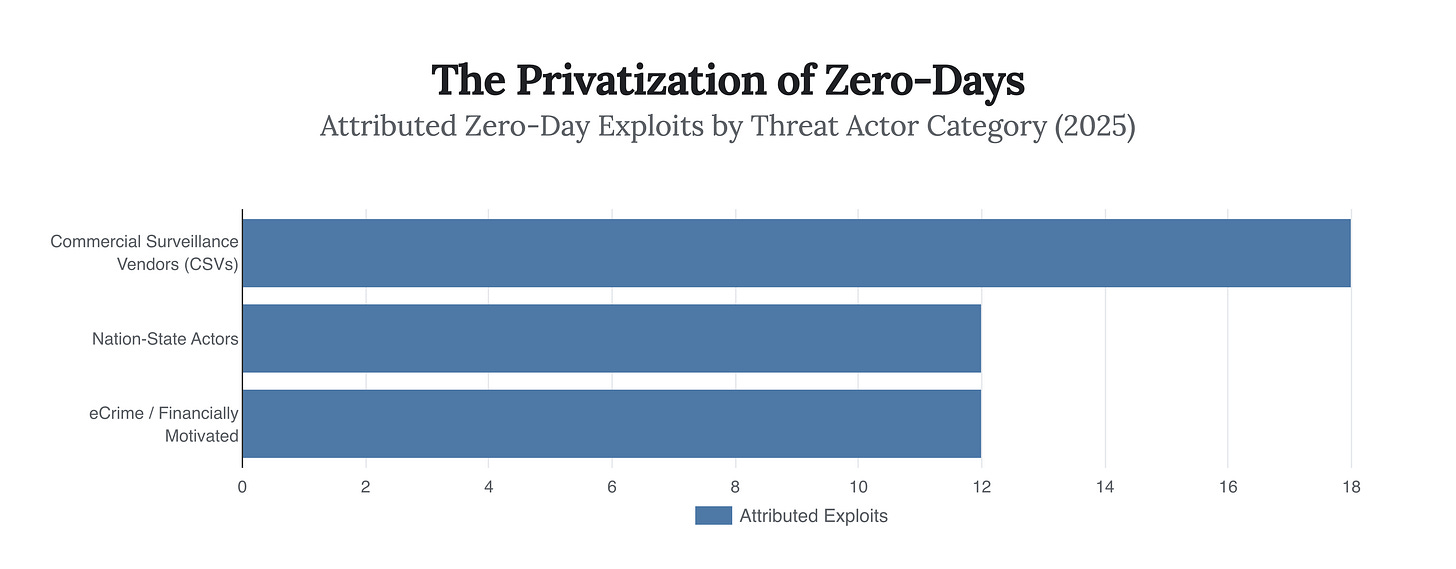
Historically, the most devastating digital weapons—zero-day exploits—were tightly guarded state secrets. These vulnerabilities, unknown to the software vendor and possessing no patch, were the exclusive domain of elite nation-state intelligence agencies. But as we parse the 2025 and 2026 data, a chilling democratization has occurred.
In 2025, security researchers tracked 90 zero-day vulnerabilities actively exploited in the wild. However, the source of these exploits marked a watershed moment in the history of cyber warfare. For the first time, Commercial Surveillance Vendors (CSVs)—private companies that legally develop and sell military-grade spyware to government clients worldwide—surpassed traditional state-sponsored groups in attributed zero-day exploitation. CSVs were responsible for 18 attributed exploits, compared to just 12 from nation-state actors.
Commercial surveillance vendors—companies legally selling spyware to government clients worldwide—have now officially surpassed nation-state intelligence agencies as the primary engines of zero-day exploitation.
This privatization of zero-days shifts the global risk profile entirely. A zero-day exploit for a major enterprise platform is no longer held in reserve for high-stakes espionage; it is a commoditized asset, frequently sold to the highest bidder or leaked into the broader criminal ecosystem. We are seeing this play out in real time in Q1 2026, with actors like APT28 weaponizing a Microsoft Office zero-day (CVE-2026-21509) alongside critical flaws in enterprise infrastructure like Cisco Catalyst SD-WAN (CVE-2026-20127).
The 2026 Sector Heatmap: Who Bleeds First?
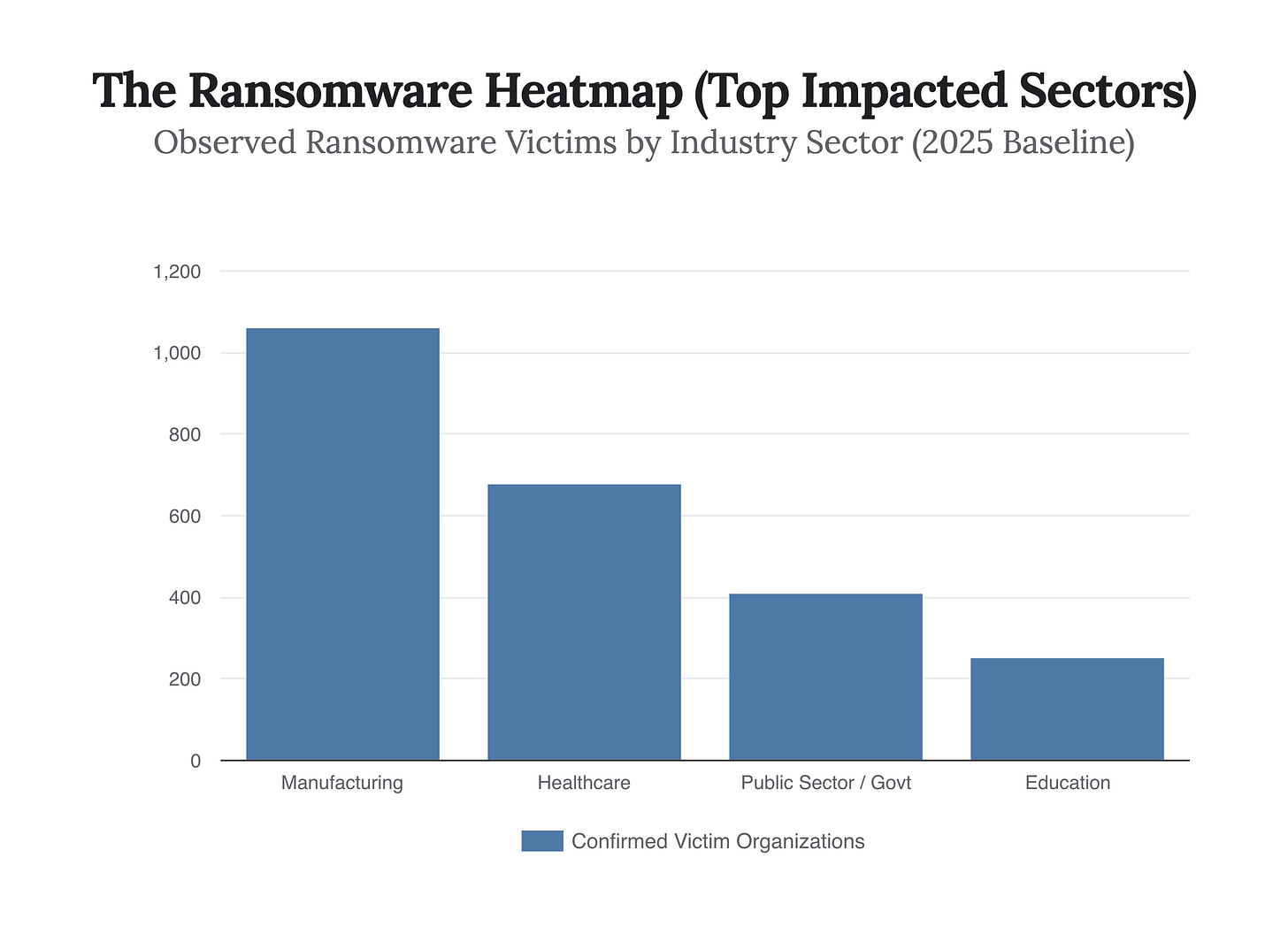
When the barrier to entry drops and the weaponry becomes elite, threat actors operate as purely rational economic agents. They target sectors where the cost of operational downtime vastly exceeds the cost of a ransom payment.
The 2025 and Q1 2026 attack heatmaps reveal a brutal concentration of fire. Discrete manufacturing emerged as the most impacted sector, representing 14% to 22% of all observed ransomware attacks, with over 1,060 observed victims in the previous year alone. A manufacturing plant running on legacy OT (Operational Technology) systems cannot afford a week of offline production; the supply chain cascading effects are too severe. Consequently, their propensity to pay astronomical ransoms makes them the prime target.
Equally alarming is the ongoing siege of the public sector. The first half of 2025 saw a 65% year-over-year increase in ransomware incidents affecting government bodies, a trajectory that has relentlessly continued into early 2026. Furthermore, 251 educational institutions were struck globally in 2025, with an average breach cost surging to $3.8 million per incident. The underlying logic is simple: municipalities and higher-education networks historically lack the massive capital expenditures required to maintain state-of-the-art, identity-centric security architectures. They are target-rich, resource-poor environments.
Strategic Synthesis: The Containment Imperative
The human brain is wired to seek absolute safety, but in the realm of 2026 cybersecurity, absolute safety is an expensive illusion. If you accept the data—133 new vulnerabilities a day, 29-minute breakout times, and the commoditization of zero-days—then the fundamental architecture of corporate defense must change.
The old doctrine mandated patching every vulnerability based on its CVSS (Common Vulnerability Scoring System) severity. But the 2026 data reveals that only about 1% of all published CVEs are ever actually confirmed to be exploited in the wild. Blindly patching based on raw severity scores without factoring in active exploit intelligence is a misallocation of highly constrained resources. Organizations must pivot to risk-based prioritization, leveraging threat intelligence like the CISA Known Exploited Vulnerabilities (KEV) catalog, to aggressively patch the 1% of flaws that actually matter to their specific attack surface.
More importantly, defense must shift from the perimeter to the identity layer. As modern telemetry proves, threat actors no longer “hack” in; they log in using compromised credentials, automation scripts, and exposed API connections.
The cybersecurity landscape is no longer a battle of impenetrable fortresses; it is a game of containment, where assuming breach is the only mathematically sound equilibrium.
By focusing on identity verification, aggressive network segmentation, and autonomous, AI-driven containment protocols, organizations can survive the initial access. The goal is no longer to prevent the adversary from touching the outer wall. The goal is to ensure that when they inevitably break through via a newly discovered zero-day, they find themselves in an empty room, isolated, and paralyzed before their 29-minute countdown expires.