The Thermodynamics of Terror: How Heat Becomes a Weapon in the AI Age?
In the quiet, humming corridors of the world’s most advanced data centers, a fundamental shift in the physics of warfare is underway. For decades, cyber conflict was a battle of logic—code against code, encryption against brute force. But with the arrival of the NVIDIA Blackwell architecture and the 120-kilowatt server racks required to power it, the battlefield has moved from the logical to the physical. We have entered the era of the Silicon Heat Sink, where the most dangerous firewall is no longer software, but a literal, physical valve.
The catalyst for this shift is the sheer density of modern artificial intelligence. Traditional air cooling—fans blowing over heat sinks—hits a physical wall at around 20 to 30 kilowatts per rack. Beyond that, air simply cannot carry the heat away fast enough to prevent silicon from melting. The latest AI clusters, such as the GB200 NVL72, demand upwards of 120 kilowatts per rack, forcing a mass migration to direct-to-chip liquid cooling. This transition has turned the cooling infrastructure itself—pumps, coolants, and valve actuators—into mission-critical Operational Technology (OT) that, if compromised, offers attackers a kill switch more permanent than any ransomware.
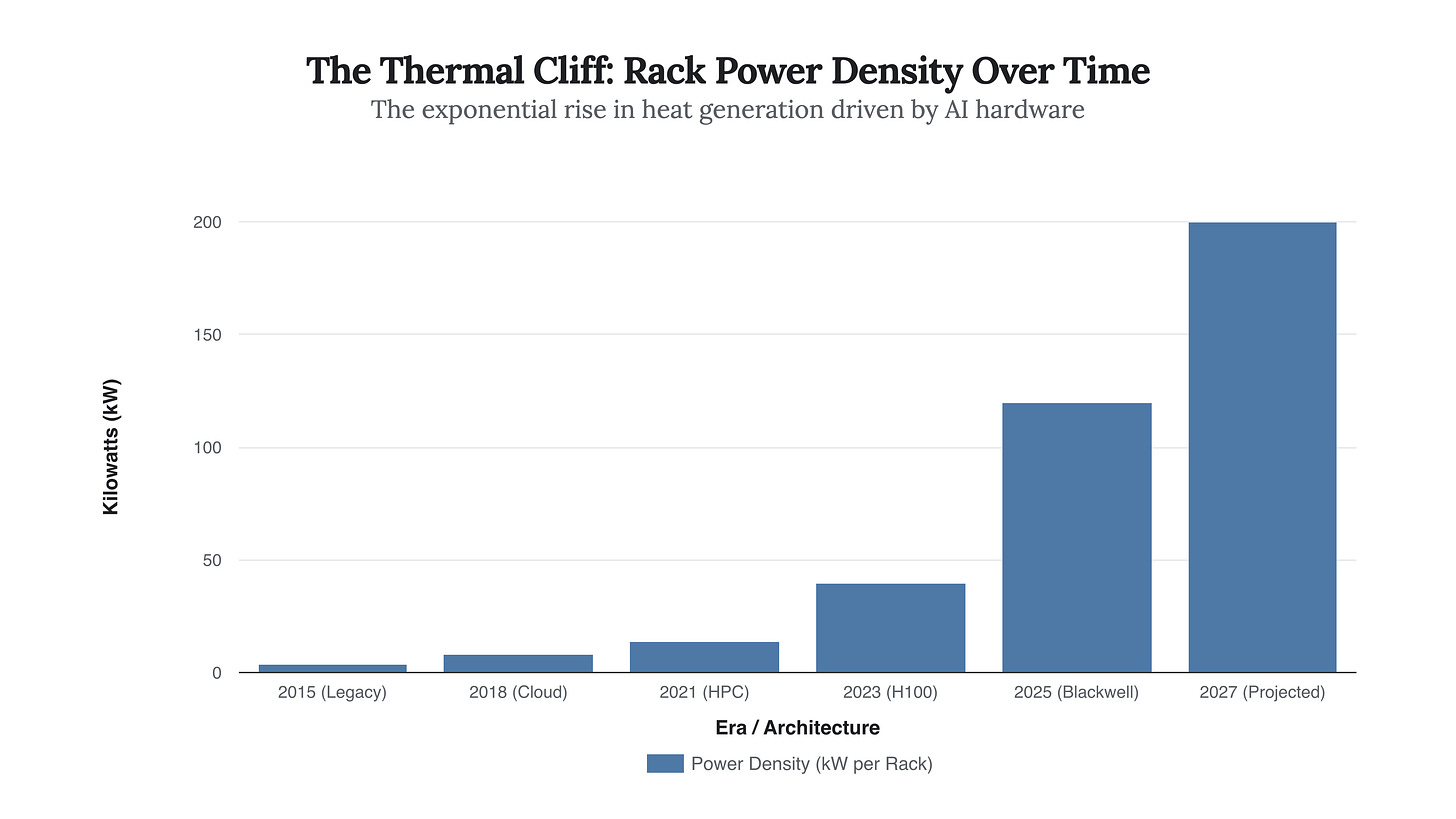
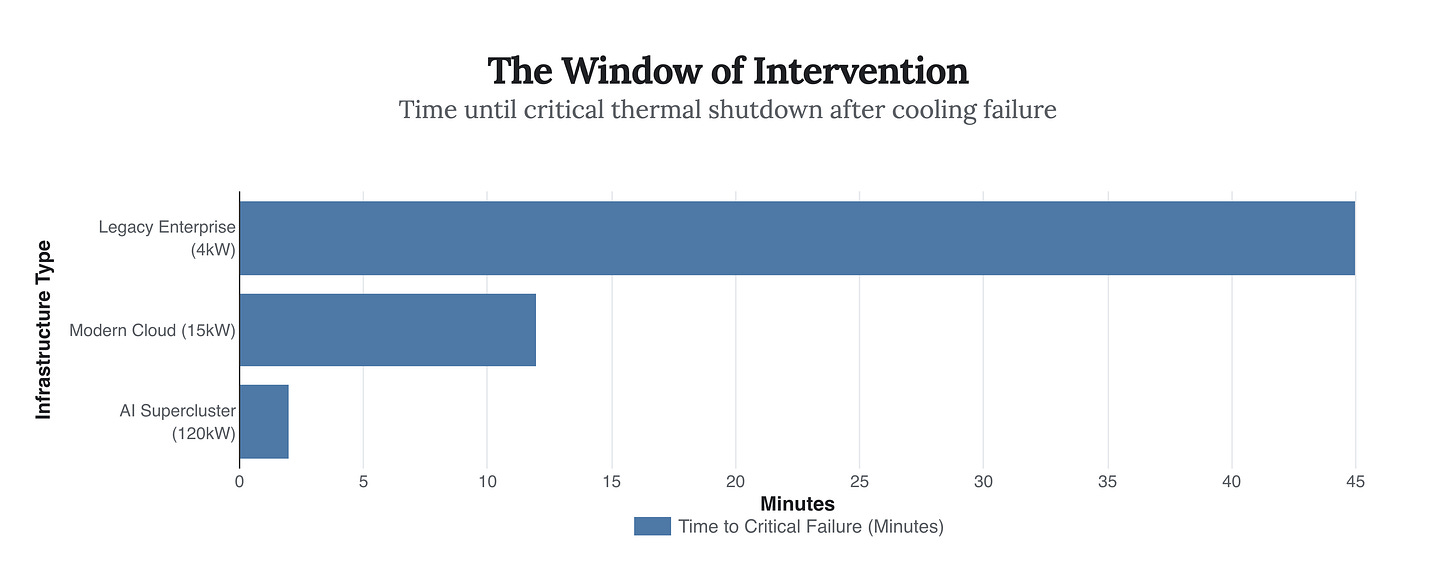
The chart above illustrates the terrifying velocity of this change. In less than a decade, the thermal load of a standard compute unit has increased thirty-fold. This is not merely an engineering challenge; it is a security crisis. In a 4kW legacy rack, a cooling failure might result in a slow temperature creep, giving administrators nearly an hour to intervene before safety shutdowns occur. In a 120kW liquid-cooled rack, the time between a pump stoppage and critical thermal failure is measured in seconds. This phenomenon, known as “thermal runaway,” effectively removes the human element from the defense loop.
Recent threat intelligence confirms that adversaries are already probing these physical systems. The sheer complexity of liquid cooling infrastructure—which requires constant telemetry from Building Management Systems (BMS) to regulate flow rates and pressures—creates a massive, often unsecured attack surface. Malware frameworks like PIPEDREAM have already demonstrated modules capable of manipulating industrial control protocols (like OPC-UA) to alter setpoints or disable safety overrides. An attacker no longer needs to steal data to cripple a nation’s AI capabilities; they simply need to convince the cooling system that a boiling server is freezing cold.
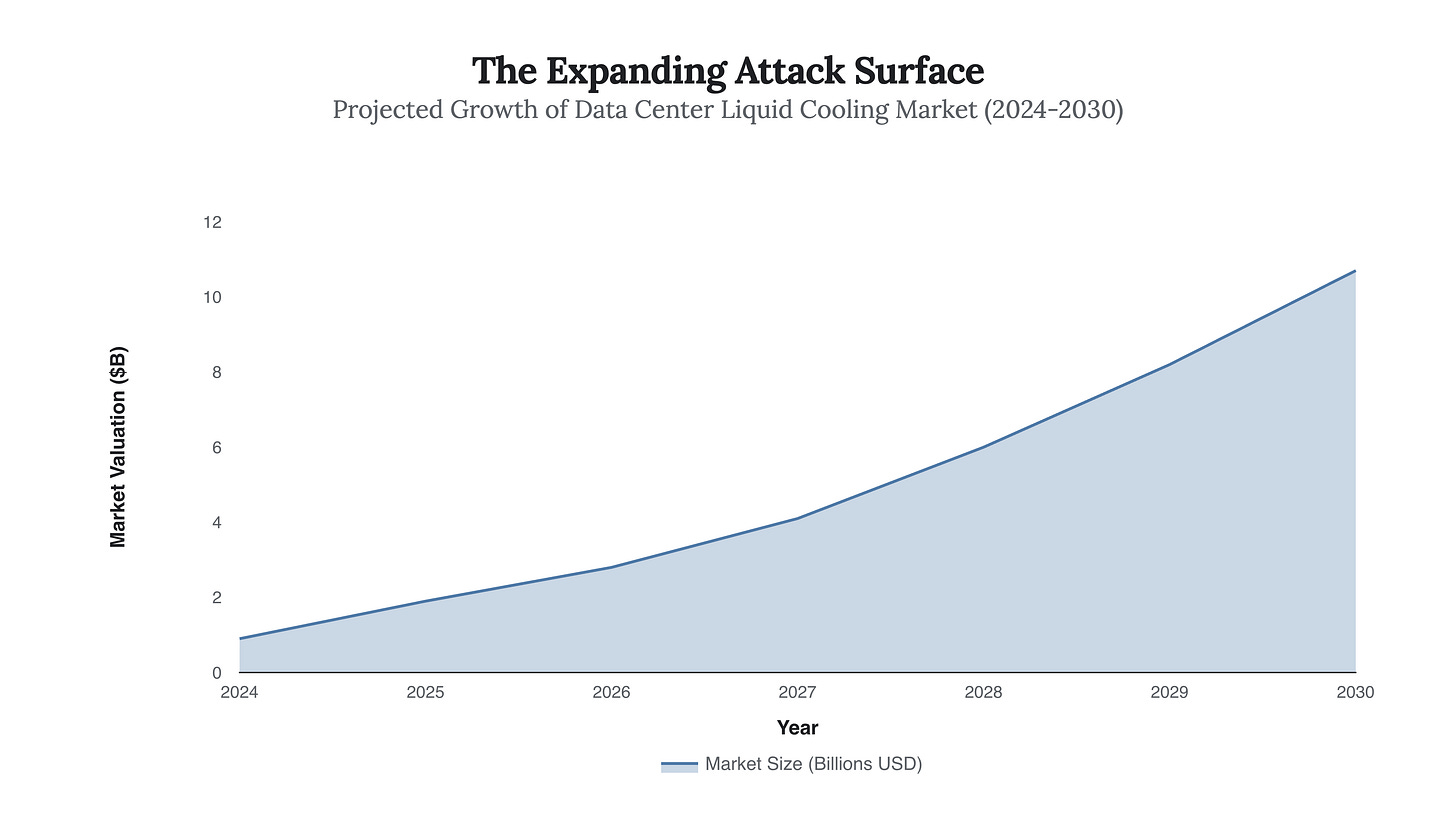
As the market for liquid cooling explodes—projected to grow from under $1 billion today to over $10 billion by 2030—so too does the vector for these kinetic cyberattacks. We are building a nervous system of pipes and pumps that is inextricably linked to the internet, often maintained by third-party vendors with security practices far less rigorous than the hyperscalers they serve. A vulnerability in a widely used coolant distribution unit (CDU) could theoretically be exploited to trigger simultaneous thermal events across multiple data centers, bypassing traditional digital redundancies.
“The primary risk of OT-focused cyberattacks is causing physical infrastructure failure... A successful attack on cooling systems could force a data hall to shut down within minutes.”
The implication is a return to a colder, more brutal form of sabotage. In 2023, a voltage sag in Australia forced a cooling shutdown that took Microsoft services offline for over 12 hours. Imagine that disruption weaponized—a coordinated attack that doesn’t just shut down the servers, but physically degrades the silicon through rapid thermal cycling. The recovery from such an attack is not a system reboot; it is a hardware replacement.
The data clearly shows the vanishing window of intervention. For the AI superclusters that will define the next decade of economic and military power, the margin for error has evaporated. We have traded thermal inertia for computational velocity, creating a fragile equilibrium where a single malicious command can result in physical destruction.
“In these high-performance data centers... thermal attacks can be more devastating than power-based attacks, making cooling not just an operational concern, but a strategic vulnerability.”
As we race toward the singularity, we must recognize that our most advanced intelligences are housed in increasingly fragile glass houses. The next great cyber weapon will not be a virus that encrypts your files, but a signal that boils the water in your pipes. In the age of AI, the ability to keep things cool is no longer just a maintenance task; it is the highest form of national defense.



Excellent analysis! Your insight that 'the battlefield has moved from the logical to the physical' is truly brilliant. It concisely highlights the paradigm shift where thermal management, now mission-critical OT, becomes such a significant security vulnerability. This physical layer attack vector is something I find trully fascinating, and concerning.