The 70% Blind Spot: Why the $180 Billion Certification Industry Fails to Stop the Root Cause of Cyber Failure
A deep dive into the dangerous divergence between compliance credentials and systems-level defense engineering
We are currently witnessing one of the most dangerous misallocations of capital in the history of information security. While the global cybersecurity market barrels toward a projected $500 billion valuation, a quiet but catastrophic rot has taken hold at the foundation. We are minting an army of “paper tigers”—professionals laden with acronym-heavy certifications who can quote NIST 800-53 chapter and verse but cannot identify a buffer overflow in a kernel dump. The industry has become obsessed with the bureaucracy of defense, effectively outsourcing the physics of defense to a shrinking pool of systems engineers.
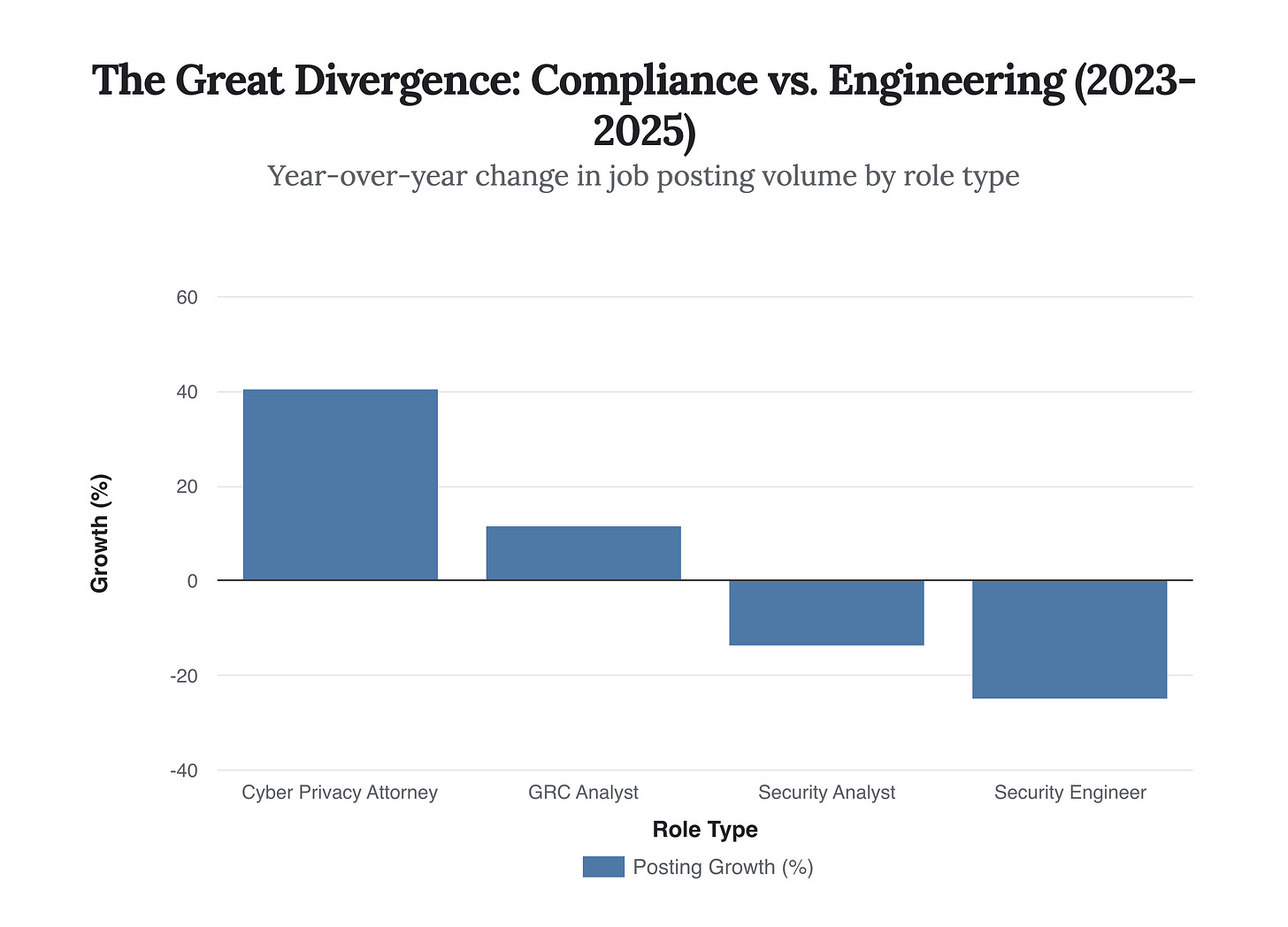
The latest intelligence from 2025 paints a stark picture: while job postings for compliance and privacy attorneys have surged by over 40%, demand for core security engineers has contracted by nearly 25%. This divergence is not merely a labor market quirk; it is a strategic failure. We are building a Maginot Line of compliance paperwork while the enemy tunnels underneath through memory-unsafe code. This briefing deconstructs the “Certification Bubble” and exposes why the current obsession with credentials is masking a critical, existential shortage in fundamental systems-level engineering talent.
The Compliance-Industrial Complex
The cybersecurity industry has bifurcated into two distinct realities: the world of checking boxes and the world of building systems. The former is booming; the latter is in a state of atrophy. Driven by an increasingly complex regulatory web—from the SEC’s breach disclosure mandates to the EU’s NIS2—organizations are prioritizing hires who can navigate legal frameworks over those who can harden infrastructure.
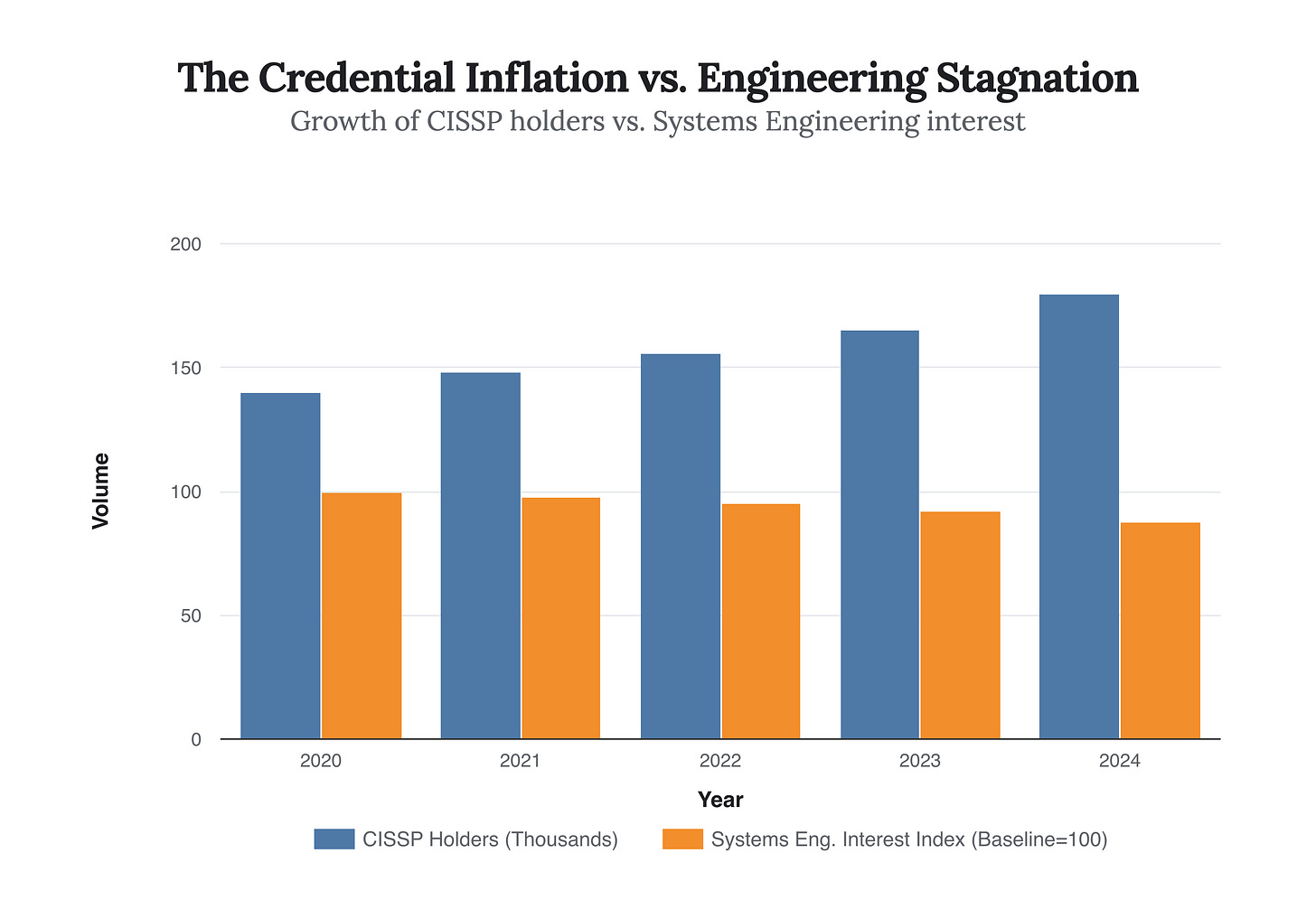
This shift has fueled a certification bubble of immense proportions. The market for cybersecurity certifications is growing at a CAGR of over 12%, flooding the entry-level market with candidates who possess theoretical knowledge of “risk frameworks” but lack the tactile engineering skills to mitigate technical risk. Human Resources departments, overwhelmed by applicant volume, use these certifications as primary filters, effectively disqualifying capable engineers who lack the “Certified” label while fast-tracking those who have mastered the art of the multiple-choice exam.
Figure 1: Data aggregated from 2024-2025 workforce reports reveals a disturbing trend: the market is aggressively hiring for legal and compliance cover (up 40%) while shedding the very engineering roles (down 25%) required to build secure systems.
The “Paper Tiger” Phenomenon
The result is a workforce hollowed out at the core. Hiring managers report a paradox: a flood of applicants for every open “Cyber Analyst” position, yet a desperate, unfilled void for “Systems Security Engineers.” The candidates arriving from bootcamps and certification mills are trained to operate tools—SIEM dashboards, vulnerability scanners, and ticketing systems. They are not trained to understand the machine. When a scanner flags a vulnerability, they can file a ticket; they cannot patch the firmware, rewrite the unsafe C function, or architect a memory-safe replacement.
The 70% Engineering Reality
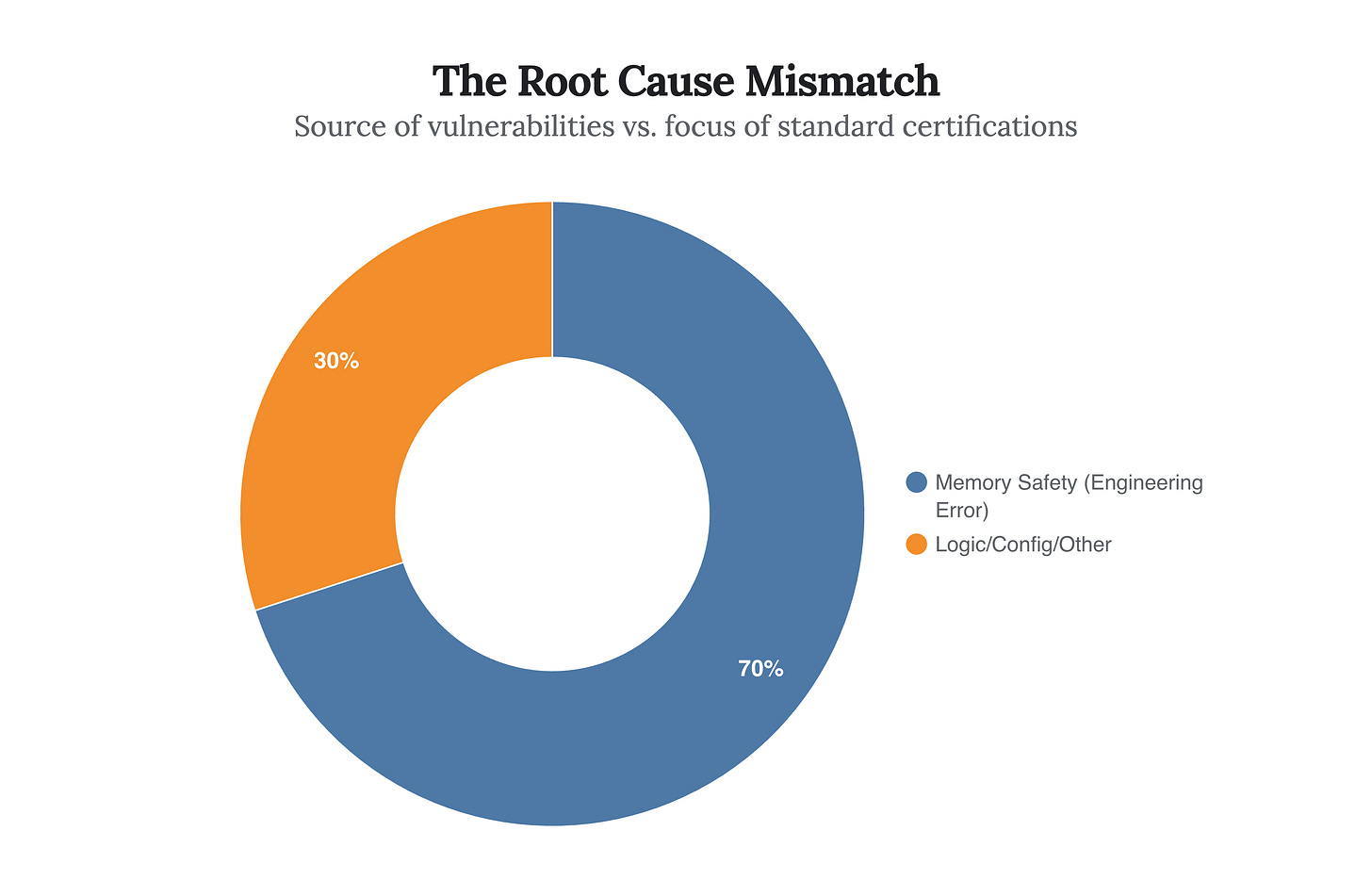
The tragedy of this skills misalignment is quantifiable. For over a decade, major technology stewards including Microsoft, Google, and the CISA have reported a consistent, stubborn statistic: approximately 70% of all severe vulnerabilities are caused by memory safety issues. These are not compliance failures. They are not policy violations. They are engineering defects—failures in pointer arithmetic, buffer management, and memory allocation in languages like C and C++.
No amount of GRC (Governance, Risk, and Compliance) paperwork can fix a use-after-free bug. Yet, the vast majority of the industry’s training budget is funneled into certifications that do not touch a single line of code. We are fighting a kinetic war against code execution exploits with the administrative weapons of policy management.
Figure 2: Despite memory safety issues accounting for 70% of severe vulnerabilities (CVEs), the standard curriculum of the most popular certifications (CISSP, CISM, Sec+) dedicates near-zero time to low-level memory management or secure coding practices.
The Atrophy of Systems-Level Defense
While the industry distracts itself with credentials, the talent pipeline for systems-level engineering is drying up. The allure of high-level abstractions—Web3, AI modeling, and React frameworks—has drawn computer science graduates away from the “hard” engineering of kernels, embedded systems, and bare-metal programming. We are producing software developers who view memory management as an artifact of the past, handled by the garbage collector.
The “Rust Belt” of Tech
This skills gap is creating a “Rust Belt” in the technology stack—not a geographic decline, but a structural decay in the lower layers of our infrastructure. Critical systems in aerospace, defense, medical devices, and industrial control systems (ICS) rely on C and C++ codebases that are decades old. Securing these requires deep intimacy with processor architecture and assembly language—skills that are rapidly becoming arcane arts. The transition to memory-safe languages like Rust is the obvious technical solution, but it is stalled by a lack of human capital capable of bridging the gap between legacy C and modern safety paradigms.
Figure 3: While the population of certified professionals climbs steadily, interest and enrollment in low-level systems engineering and embedded disciplines shows a concerning decline, creating an inverse relationship between credentialed supply and technical capability.
Strategic Implications: The Fragility of Critical Infrastructure
The geopolitical implications of this talent shortage are profound. Adversaries, particularly state-sponsored actors, are not targeting compliance checklists; they are targeting zero-day vulnerabilities in firmware and edge devices. The “Volt Typhoon” campaigns and similar nation-state activities demonstrate a focus on living-off-the-land in OT (Operational Technology) environments where “Cyber Security Analysts” are often powerless.
We are entering an era where the primary defense constraint is not budget, but engineering bandwidth. Organizations may have the funds to hire, but they cannot find the individuals capable of doing the work. This leads to a dangerous reliance on “black box” security tools—purchasing protection rather than building resilience. It works until the tool itself is compromised, as seen in the SolarWinds and more recent supply chain attacks.
“We don’t actually have a talent shortage in cybersecurity. We have a shortage of the right people with the right skills. We have plenty of analysts; we are starving for engineers.” — Analysis of 2025 SANS Workforce Data
Future Outlook: The Correction Must Be Technical
The bubble will burst, or rather, it will deflate as the market corrects. The “Secure by Design” initiative pushed by CISA and the ONCD (Office of the National Cyber Director) signals the end of the compliance-first era. Regulatory pressure is shifting from “did you check the box?” to “did you build it safely?” This will force a radical realignment of the labor market.
Predictions for 2026-2027
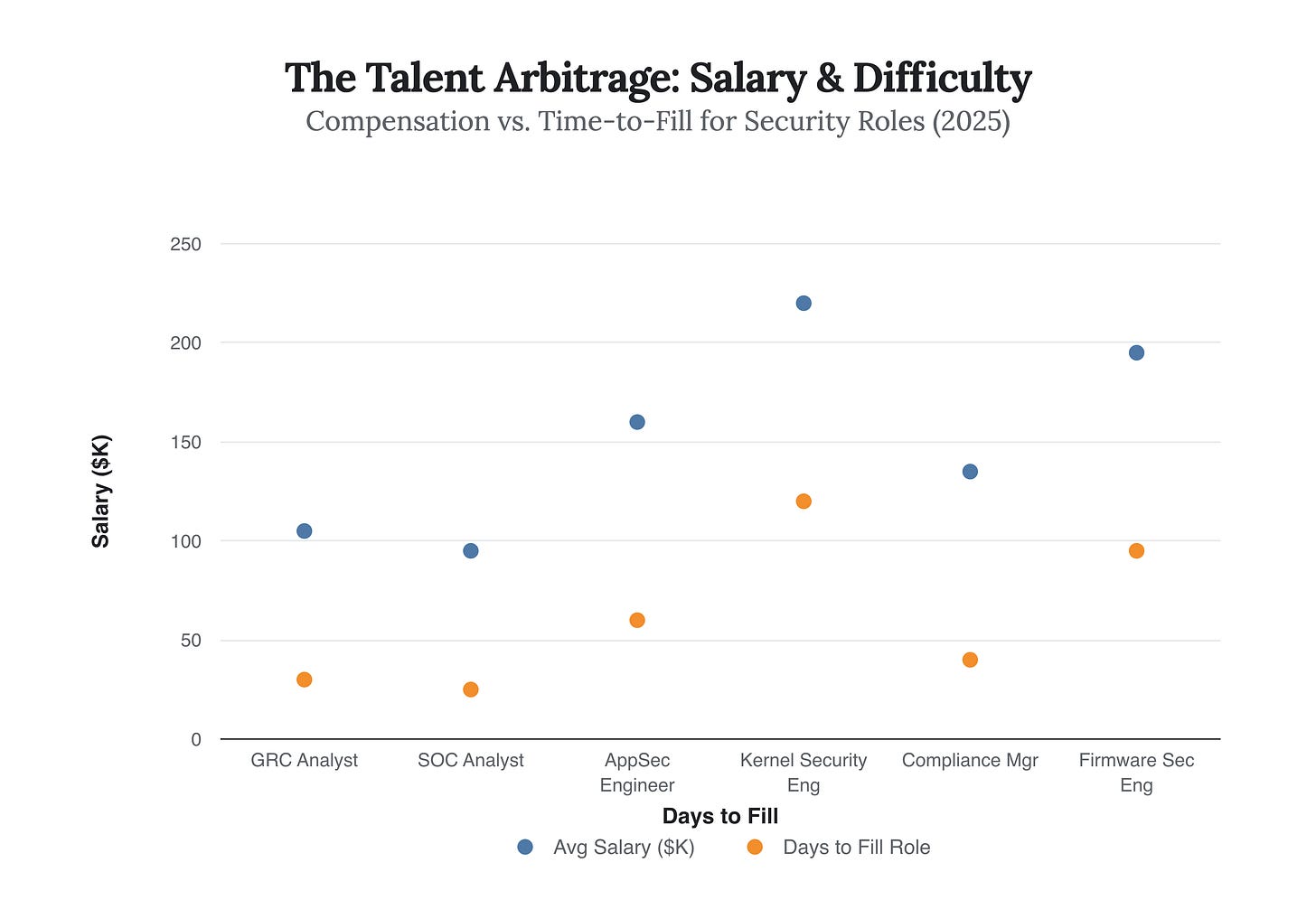
The Rise of the “Security Engineer” over the “Cyber Pro”: Salaries for kernel-level security engineers and firmware security specialists will decouple from the general IT security market, likely commanding 50-70% premiums over generalist analyst roles.
Certification Devaluation: Entry-level certifications will lose their potency as hiring filters. innovative companies will move to practical, engineering-based assessments (e.g., “Fix this vulnerable code block”) rather than keyword matching.
The Rust Renaissance: The demand for Rust developers will outstrip supply by a factor of 10:1 as the “memory safe” mandate moves from federal guidance to commercial requirement.
Figure 4: A clear arbitrage opportunity exists. Engineering roles (Blue) take significantly longer to fill and command higher salaries, reflecting true scarcity, while Compliance/Ops roles (Red) are liquid and saturated.
To navigate this shift, leaders must stop treating cybersecurity as an IT problem or a legal problem. It is an engineering problem. The solution is not to hire more people who can read the map; it is to hire people who can fix the engine. The era of the paper tiger is ending; the era of the builder must return.
The single most important strategic insight is this: If 70% of your risk comes from engineering flaws, and 90% of your training budget goes to compliance certifications, you are financing your own failure.