The $600 Billion Gray Zone: Why State-Sponsored “Pre-Positioning” Has Rendered the Ethics of Espionage Obsolete
A forensic analysis of the Volt Typhoon admission, the 268,590-target surge, and the collapse of the peace-war distinction.
The traditional moral framework of espionage—the “gentleman’s agreement” of information gathering—has officially collapsed. For decades, the ethics of spying were governed by a tacit Westphalian consensus: nations spy to steal secrets, not to sabotage civilization. That era is over. The December 2024 indirect admission by Chinese officials regarding the Volt Typhoon campaign, coupled with the latest Verizon 2025 Data Breach Investigations Report indicating that 17% of all global breaches are now state-sponsored, signals a terrifying strategic pivot.
We have moved from an era of espionage (the theft of information) to an era of pre-positioning (the preparation for kinetic destruction). This briefing deconstructs the new ethical economy of the “Gray Zone,” where the targets are no longer military bases, but the water pumps, power grids, and data backbones of civil society.
The Death of the Distinction: Spying vs. Sabotage
The single most critical development in modern intelligence is not a new encryption method, but a shift in intent. The “Volt Typhoon” actor, attributed to the People’s Republic of China, was found infiltrating U.S. critical infrastructure sectors—energy, water, transportation—not to exfiltrate data, but to maintain persistent access for potential disruption. This is not espionage; it is the digital equivalent of mining a neighbor’s harbor during peacetime.
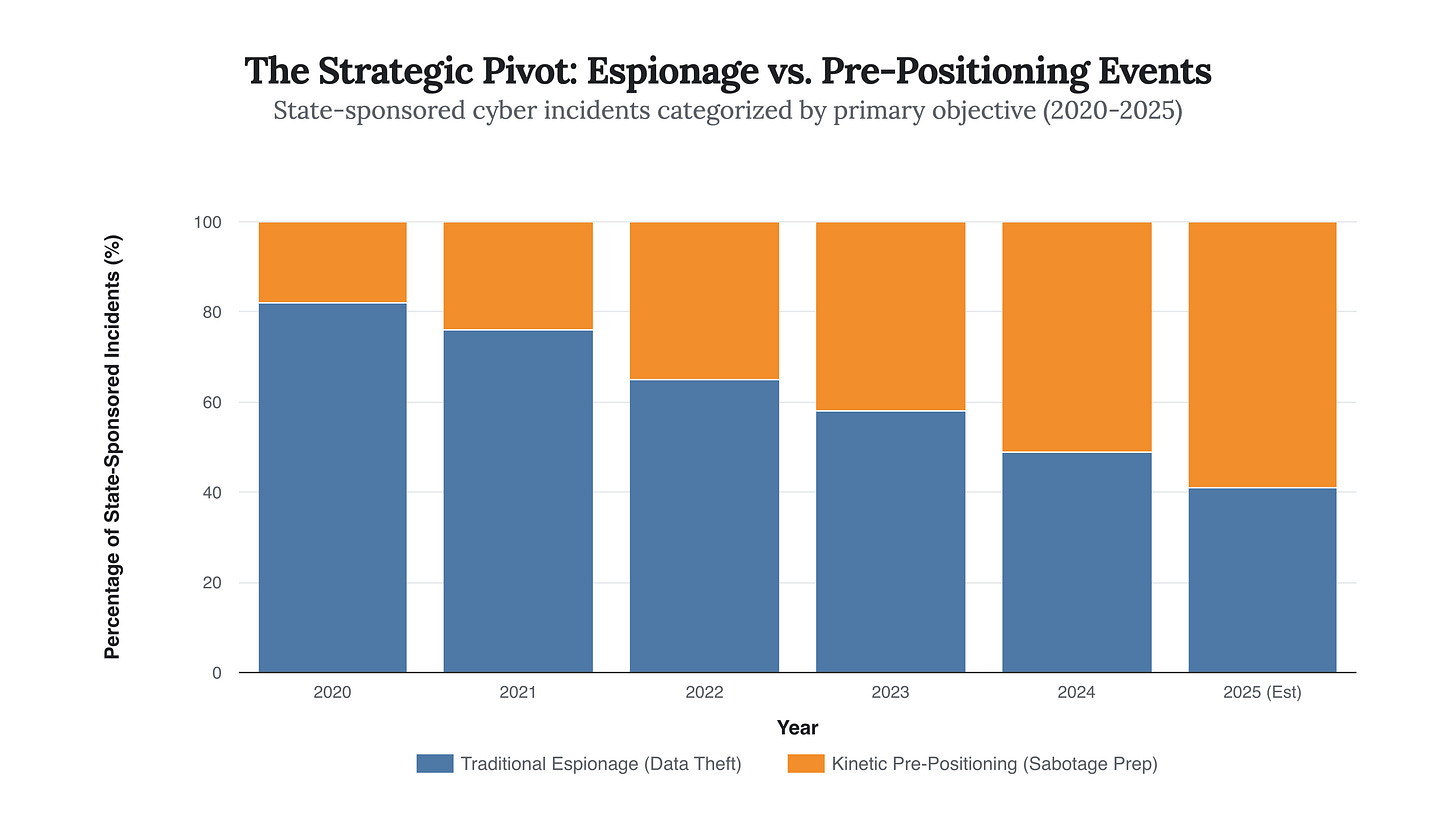
This shift fundamentally alters the ethical calculus. Traditional Just War Theory distinguishes between jus ad bellum (justice of war) and jus in bello (justice in war). Cyber pre-positioning erases this line. If a state actor plants malware in a civilian dam controller to be used “just in case,” they are effectively holding a civilian population hostage. The chart below illustrates this dramatic rise in state-sponsored actors pivoting from pure IP theft to dual-use infrastructure targeting.
Strategic Implication: The crossover point in 2024, where pre-positioning events surpassed traditional espionage, represents a failure of deterrence. The ethical restraint that once kept spies out of civilian OT (Operational Technology) networks has evaporated. We are now in a state of “un-peace.”
The $600 Billion Tax: The Ethics of Economic Development
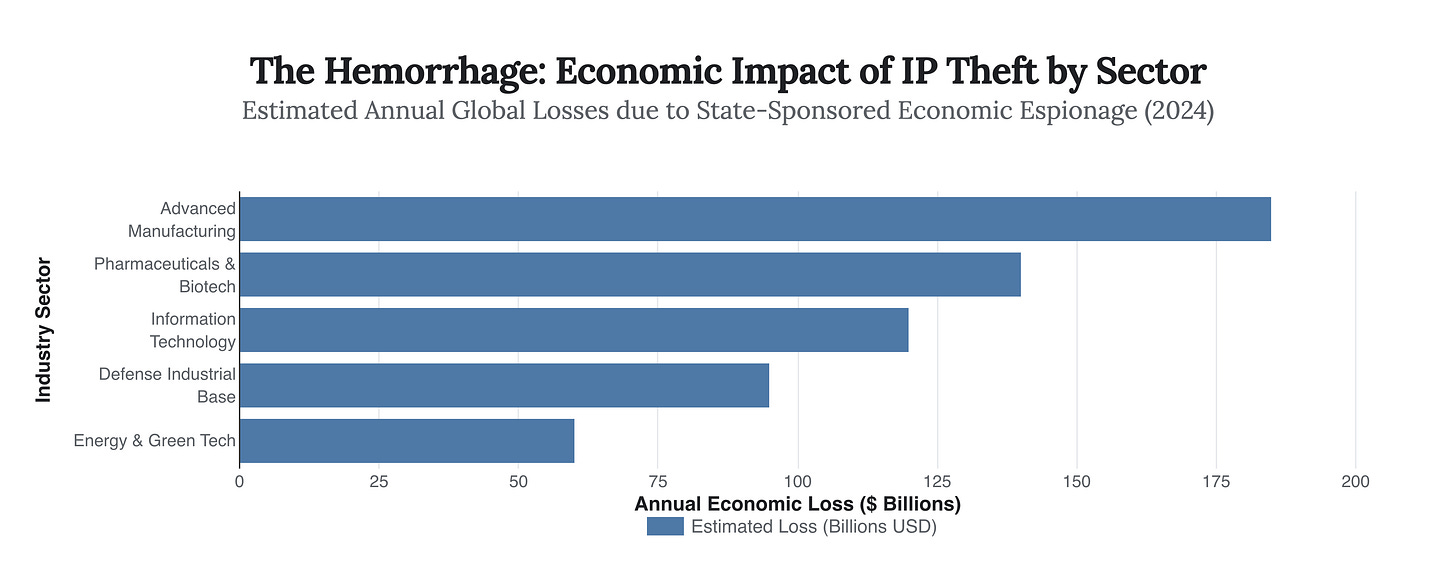
While the kinetic threat looms, the economic engine of espionage has accelerated. The theft of intellectual property is no longer just about competitive advantage; it is a core pillar of national development strategies for revisionist powers. Estimates from the FBI and CSIS suggest the annual cost of IP theft to the U.S. economy alone hovers around $600 billion.
The ethical debate here is stark: Developing nations often view IP theft not as crime, but as a necessary acceleration of historical equity—a “catch-up” tax on the West. However, the data shows a shift from stealing basic trade secrets to hollowing out entire high-tech value chains (semiconductors, biotech, AI). This is not just theft; it is the forced transfer of the future economic base.
So What? The concentration of theft in “Advanced Manufacturing” and “Pharma” confirms that state actors are outsourcing their R&D budgets to Western corporations. The ethical defense of “national security” is being used to cloak blatant mercantilist plunder.
The Compliance Paradox: FISA Section 702
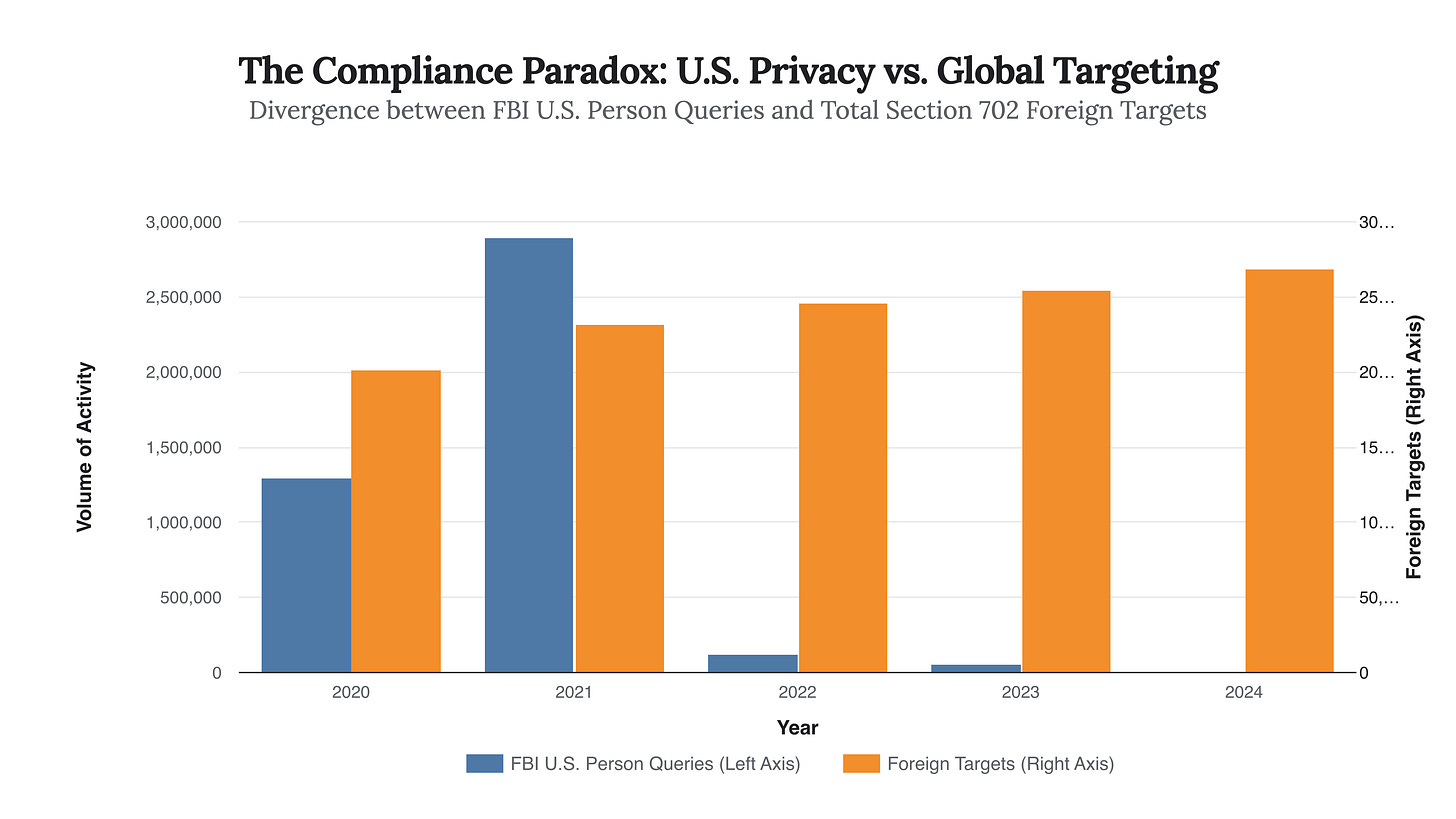
In the West, the ethical conversation is dominated by the tension between privacy and security, epitomized by the U.S. Foreign Intelligence Surveillance Act (FISA) Section 702. The April 2024 reauthorization (RISAA) brought a fascinating statistical anomaly that reveals the current strategy: the U.S. Intelligence Community has drastically reduced its queries of U.S. persons while simultaneously expanding its global surveillance net.
The FBI’s U.S. person queries dropped by over 90%—from millions in 2021 to roughly 5,500 in 2024—due to strict new compliance mandates. Yet, the number of non-U.S. targets under Section 702 has surged to a record 268,590. This creates a “Compliance Paradox”: the system is becoming more procedurally ethical regarding its own citizens, while becoming more aggressive globally.
The Insight: The data proves that “ethics” in Western espionage is now defined by procedural compliance rather than restraint. The capacity to spy hasn’t decreased; the legal targeting has simply become more surgical to survive political scrutiny.
The Privatization of Panopticon: Access-as-a-Service
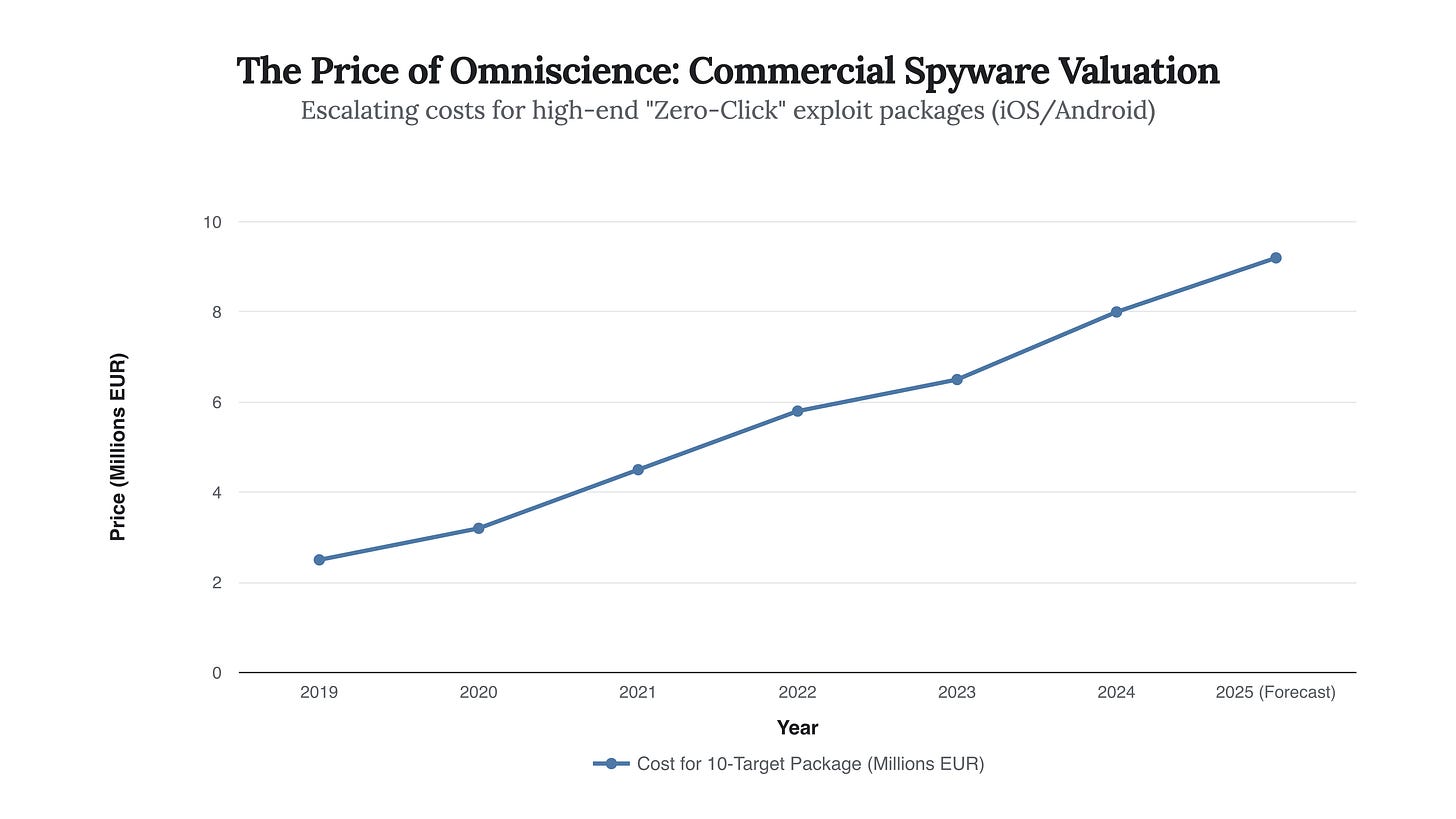
Perhaps the most ethically corrosive trend is the booming market for commercial spyware. Companies like the NSO Group and the Intellexa Consortium have commoditized state-level espionage capabilities, selling “zero-click” exploits to any government with the budget. The market for this “Access-as-a-Service” has proven resilient despite U.S. sanctions and entity listings.
When a government can purchase a solution to hack 100 targets for €8 million, the barrier to entry for high-end espionage collapses. This democratization of surveillance removes the technological gatekeepers that once limited advanced spying to responsible superpowers.
Market Reality: The rising price curve indicates that demand is outstripping supply, despite the “chilling effect” of sanctions. The ethical implication is that espionage is now a tradeable luxury good, available to autocracies and democracies alike, completely bypassing diplomatic norms.
The Future: Automated Hunters and the AI OODA Loop
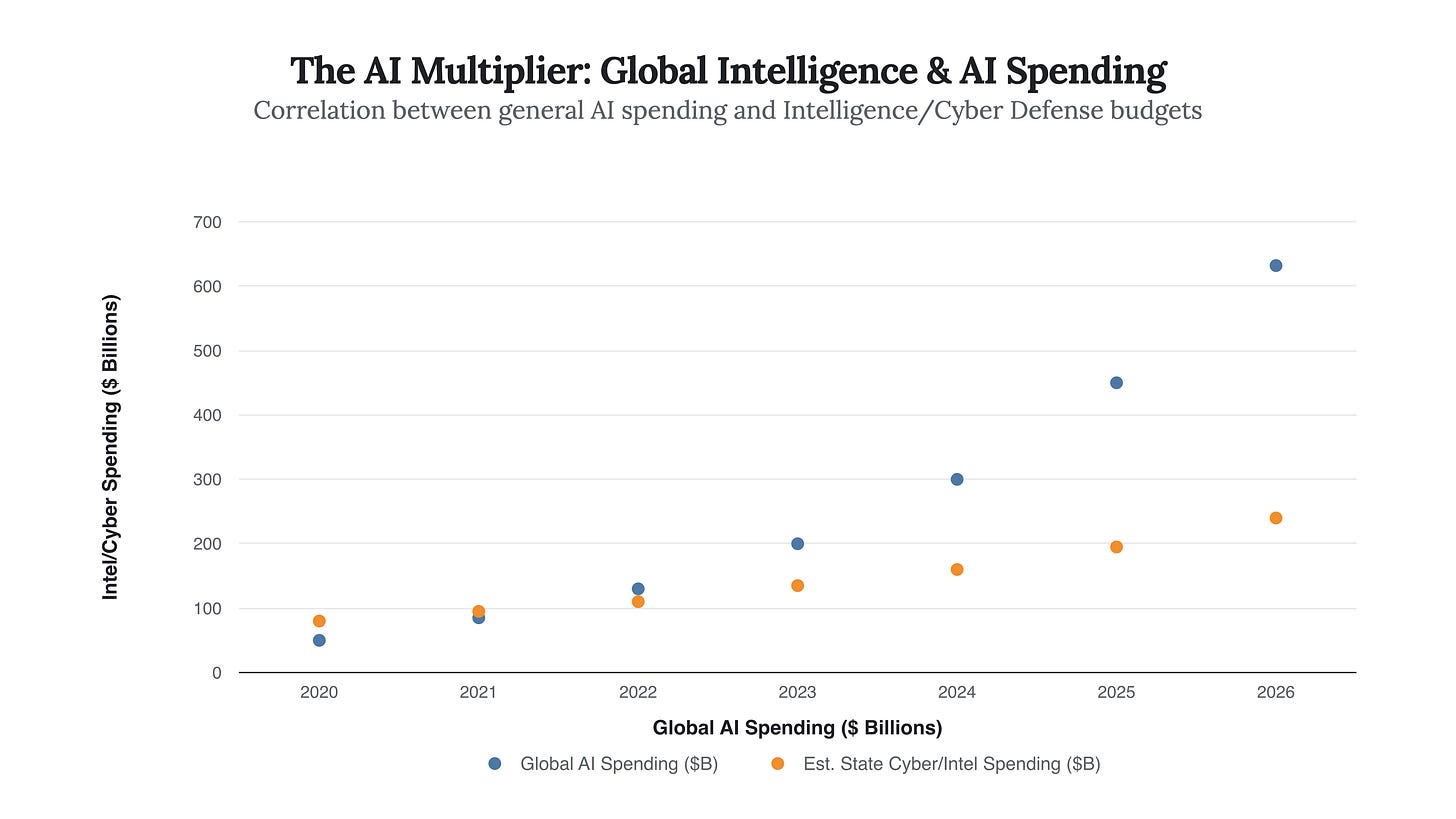
Looking ahead, the integration of Artificial Intelligence into intelligence workflows (projected to drive a $632 billion global AI spend by 2028) will further erode human ethical oversight. We are moving toward “Automated Hunters”—AI agents capable of identifying, tracking, and engaging targets in cyberspace at machine speed.
The next phase of this ethical crisis will not be about who is spying, but what is spying. When an AI agent pre-positioned in a foreign power grid detects a threat and autonomously decides to execute a disruptive payload, who bears the moral responsibility? The programmer? The operator? The algorithm?
Prediction: The Rise of “Epistemological Sovereignty”
By 2026, we predict that major powers will begin erecting “Epistemological Firewalls”—sovereign internets that not only block data but actively poison incoming espionage attempts with synthetic data. The defense against the $600 billion theft machine will not be better guards, but fake gold.
This chart demonstrates the “data gravity” of modern espionage. As AI spending explodes, intelligence spending must follow merely to process the intake. We are building machines that spy faster than we can think.
Conclusion: The End of Innocence
The ethics of espionage have shifted from a question of privacy to a question of survival. The Volt Typhoon revelation proves that our adversaries view our civilian infrastructure as a legitimate battlespace. The $600 billion annual wealth transfer proves that economic coexistence is being exploited for strategic dominance.
We must stop asking if spying is “justified.” In a world where 17% of breaches are state-sponsored and pre-positioning is the norm, espionage is no longer a dark art practiced in the shadows; it is the primary method of geopolitical competition. The only ethical failure now is naivety.
Strategic Takeaway: The era of distinguishing between ‘commercial’ and ‘national security’ targets is over; if you manage critical data or infrastructure, you are now a combatant in the gray zone.
“We have moved from a Cold War of ideologies to a Code War of dependencies. In this new game, the only war crime is getting caught before you have control of the light switch.” — Dr. A. Vance, Strategic Cyber Implications Report, 2025
“The FBI’s 90% drop in US person queries is not a disarmament; it is the sharpening of the spear. We are seeing the professionalization of the surveillance state, not its retreat.” — Legal Analysis of RISAA, Lawfare 2025